Financial Services
Meeting regulatory demands is a constant challenge for financial institutions. From evolving audit requirements to strict access control mandates, staying compliant requires more than manual effort. IDHub delivers an Identity and Access Management solution designed to help finance teams automate access, enforce policy, and maintain full visibility.
IAM for Financial Regulatory Compliance
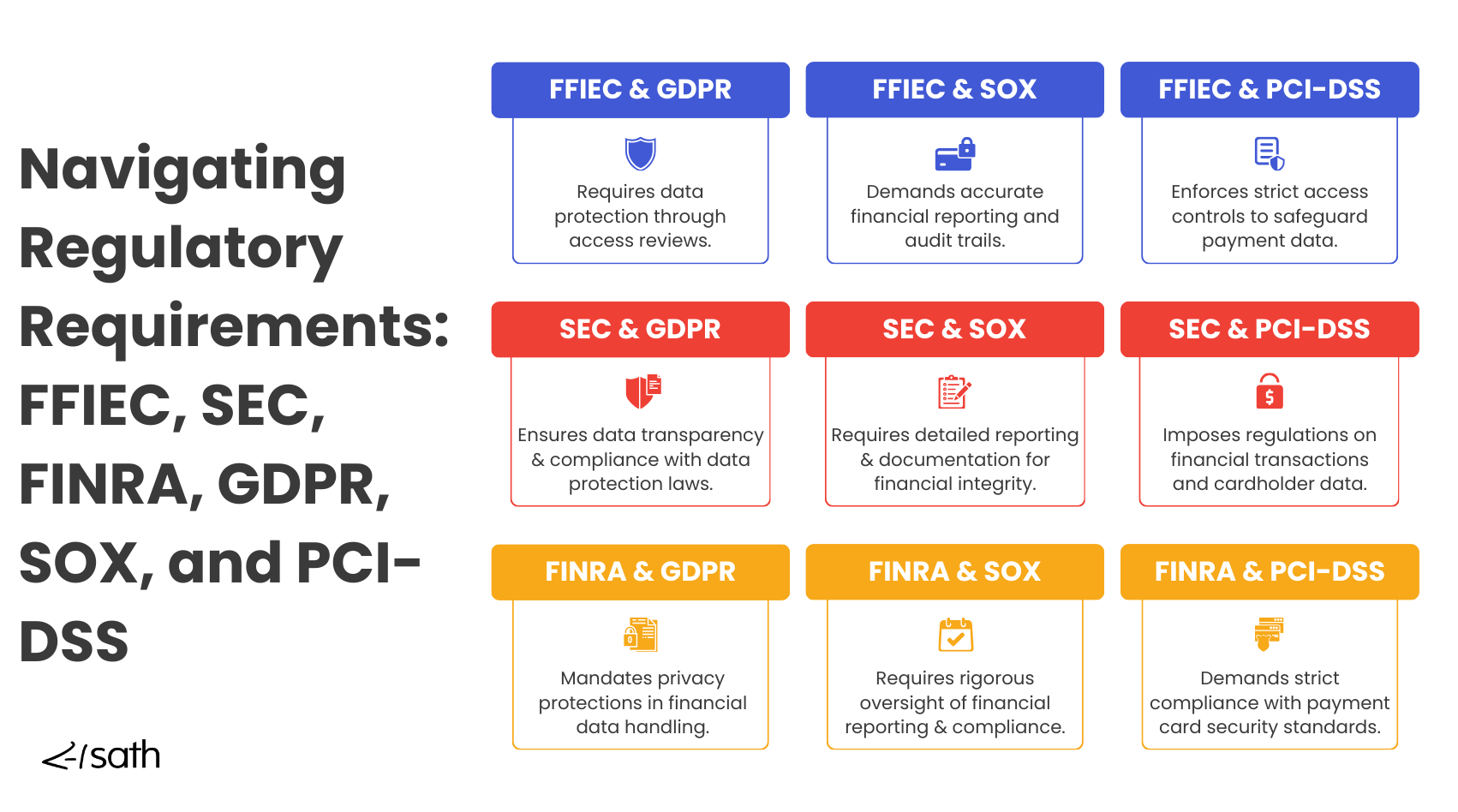
Financial institutions must comply with strict regulations like SOX, GLBA, PCI-DSS, and FFIEC to protect customer data and ensure operational integrity. These frameworks require detailed oversight of user access, strong internal controls, and provable audit trails.
Identity and Access Management (IAM) solutions like IDHub provide the foundation for meeting these mandates. By centralizing identity governance and enforcing consistent access policies, IAM helps financial organizations control risk, ensure data privacy, and maintain continuous compliance across systems and users.
Secure Access for Financial Data
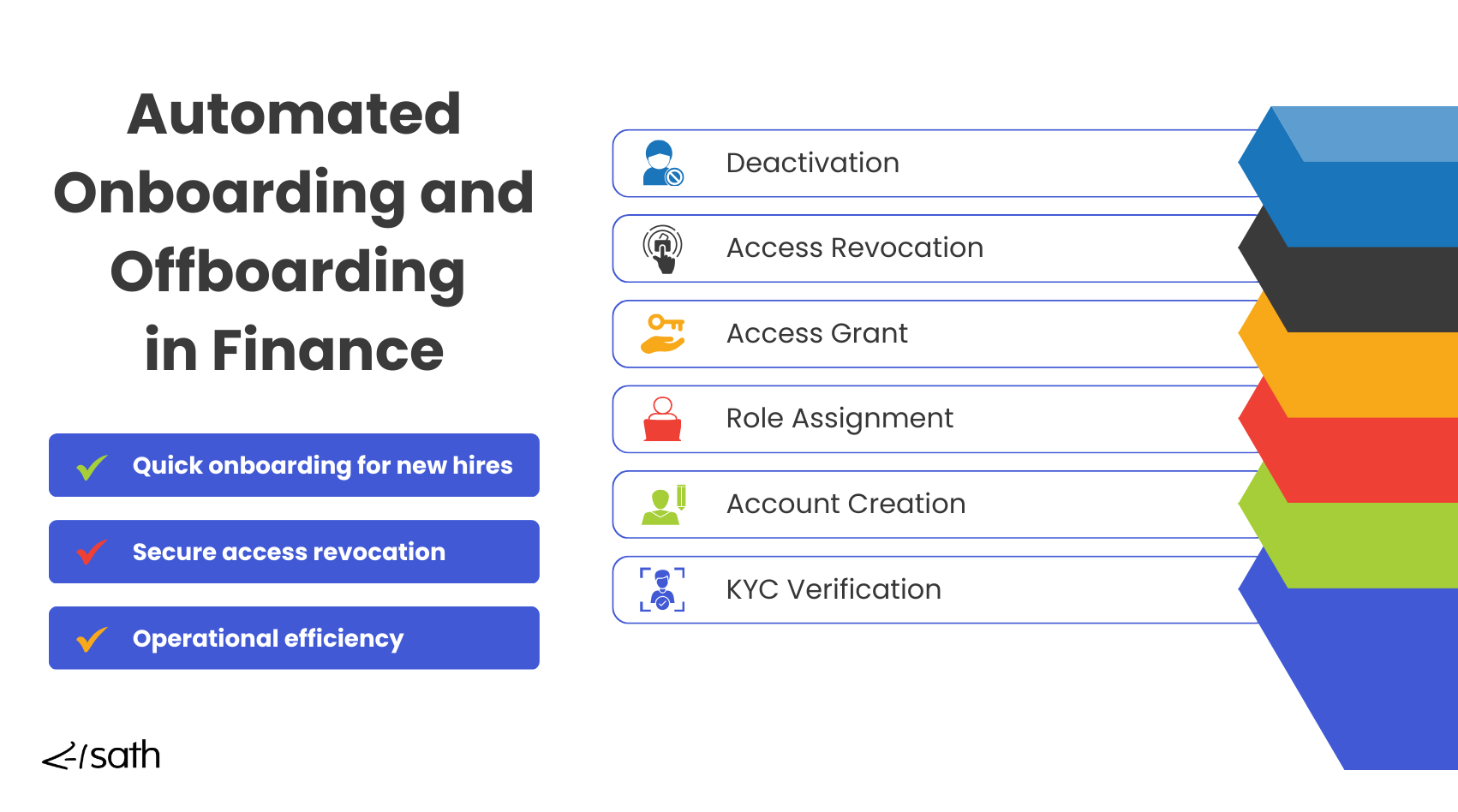
Without automation, managing user access is slow, error-prone, and non-compliant. IDHub eliminates these risks by delivering automated Identity and Access Management capabilities purpose-built for financial compliance.
Top IAM Functions for Meeting Compliance Standards
- Role-Based Access Control (RBAC): Assign access based on job function to enforce least privilege
- Automated Provisioning & Deprovisioning: Ensure timely, accurate access updates
- Access Reviews & Certification: Regularly validate access for audit readiness
- Comprehensive Audit Trails: Maintain searchable records for regulators and internal teams
- Real-Time Access Monitoring: Identify and respond to suspicious access in critical systems
IDHub helps financial institutions streamline compliance and avoid costly audit failures.
Governance
Monitor, Logging and Reporting
Track and audit user access across payment systems, with detailed logging and role-based controls to enforce transaction limits and approval hierarchies.
Multi-Factor Authentication
Email Systems and Internet Browsers
Secure email systems and web browsers without relying on passwords—manage access seamlessly through Keycloak MFA integrations.
Support
IT Desk Access Control
Manage and authenticate IT help desk activity to meet financial compliance standards and prevent unauthorized access.
Zero Trust Security for Financial Compliance
Financial institutions face growing pressure to strengthen cybersecurity and meet evolving regulatory requirements.

A Zero Trust approach—built on verifying every user and controlling every access—has become essential for reducing risk and ensuring compliance.
IDHub simplifies Zero Trust adoption with a step-by-step path tailored for financial organizations. It secures dynamic workforces, legacy systems, and third-party access without disrupting operations.
As ransomware attacks surge and regulators demand stronger controls, implementing IAM and Privileged Access Management is no longer optional.
IDHub helps banks and financial services build cyber resilience, respond to breaches quickly, and maintain trust across the financial ecosystem. In addition, it supports audit readiness by enforcing consistent access controls and detailed logging.
Reduce Cyber and Insider Threats in Finance
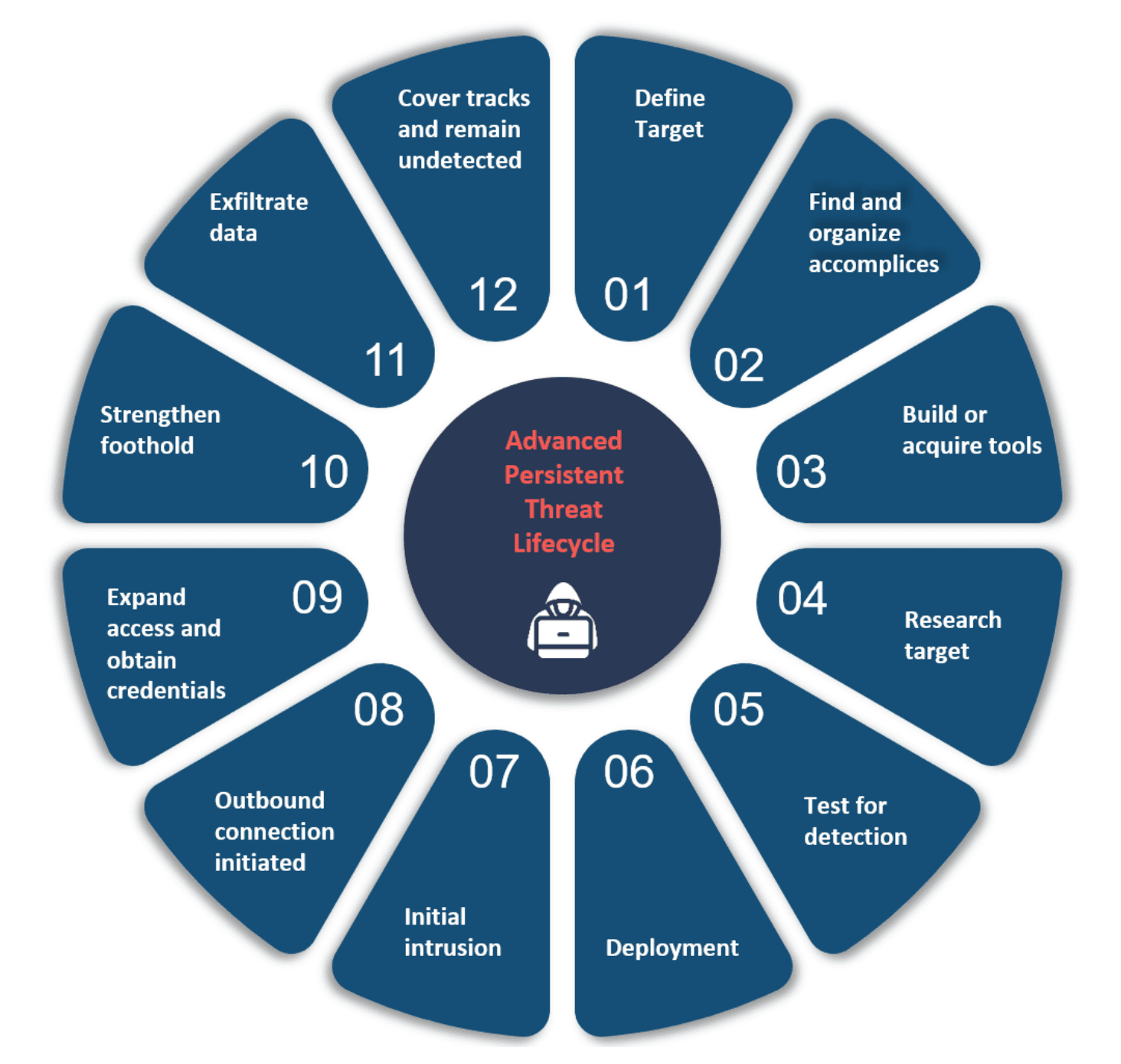
Financial institutions are top targets for cyberattacks, with breaches exposing sensitive customer and employee data. Outdated infrastructure, unpatched systems, and weak access controls increase the risk of Advanced Persistent Threats (APTs) and regulatory violations.
IDHub helps financial organizations reduce these risks by enforcing strict Access Control Policies:
- Eliminate audit fatigue with automated access governance
- Lower costs through auto-provisioning and de-provisioning
- Trigger access reviews automatically based on role or status changes
- Deliver auditor-ready reports tailored to compliance requirements
Prevent Insider Threats with IAM
Insider threats are a growing concern in regulated finance environments. Identity and Access Management (IAM) reduces this risk through Role-Based Access Control (RBAC), least privilege enforcement, and continuous monitoring.
IDHub enables rapid de-provisioning when roles change and supports Multi-Factor Authentication (MFA) for secure access. With IAM, financial institutions can meet compliance, control access, and strengthen internal defenses.
Learn how How IAM helps to mitigate insider threats for financial institutions here, or download a free PDF info-graphic to share with your team here.
20+ Years of IAM Expertise
Sath has over two decades of experience delivering Identity and Access Management solutions for highly regulated industries, including banking, insurance, and healthcare.
Our team has supported Fortune 500 organizations and mid-sized institutions alike in navigating complex compliance requirements, modernizing access governance, and reducing audit risk.
With a deep understanding of regulatory frameworks and enterprise-scale IAM, Sath is uniquely positioned to help your organization implement a secure, compliant, and future-ready access management strategy.
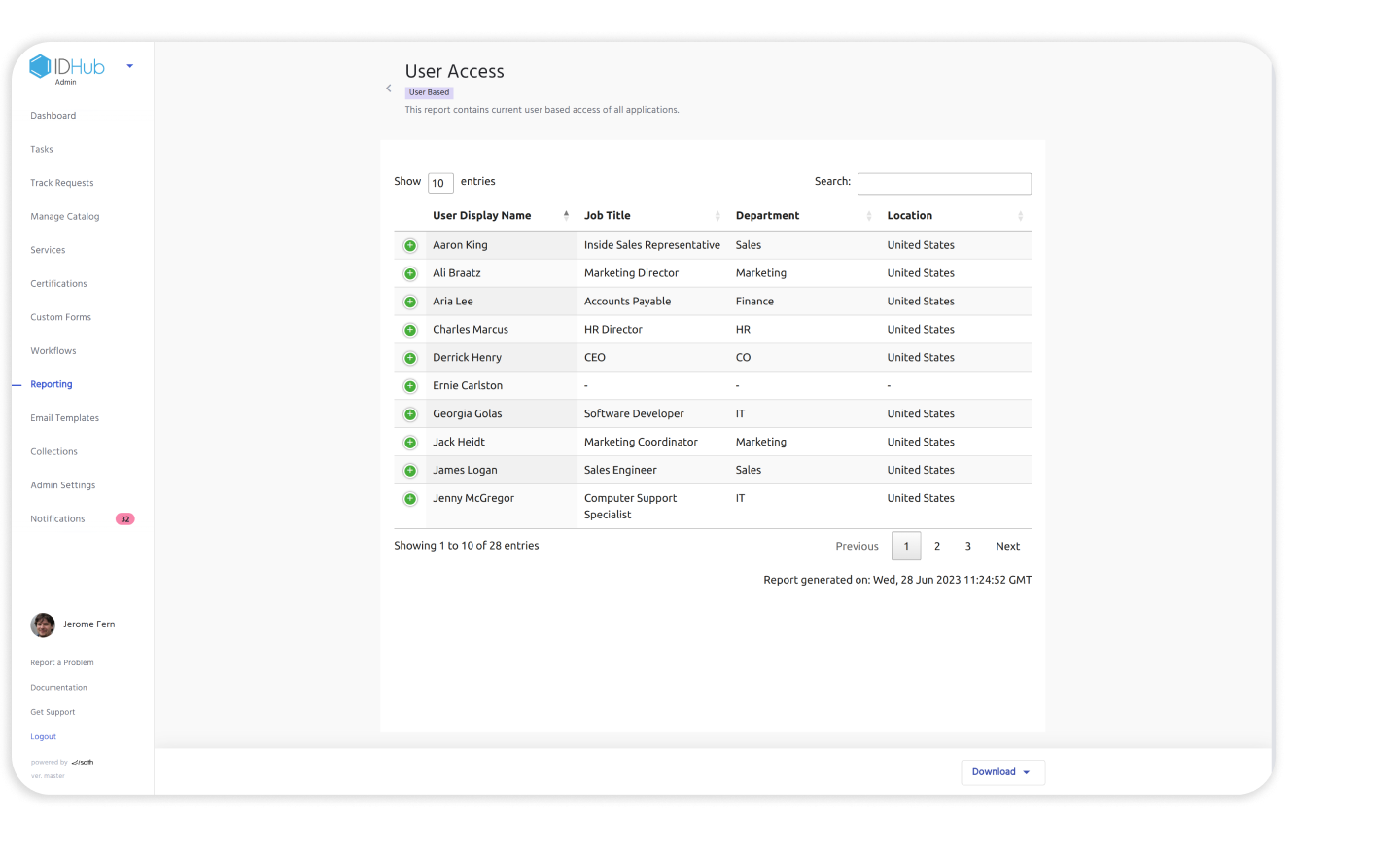
Access Review and Compliance Reporting Demo
Watch how IDHub simplifies access certification and audit reporting for financial institutions. This demo shows how to verify user access based on roles, enforce least privilege, and generate audit-ready reports in seconds—helping you meet SOX, GLBA, and other compliance requirements with ease.
Regulatory Compliance for Banks
Banks face intense regulatory scrutiny and must comply with frameworks like FFIEC, PCI-DSS, SOC 2, and GLBA. IDHub helps financial institutions stay compliant by enforcing strict access controls, automating reviews, and providing the audit-ready reporting regulators expect.
Enforce Role-Based Access for Financial Data
IDHub ties user access to specific roles and attributes, ensuring only authorized bank employees can access sensitive systems and data. This reduces the risk of over-permissioning and supports the principle of least privilege—core to regulatory compliance.
Custom Workflows Built for Bank Compliance
Banks can configure IDHub’s approval workflows to match internal policies and regulatory expectations. Whether you need dual approval for high-risk access or manager-based reviews, IDHub ensures each access request is properly routed, tracked, and approved.
Automated Access Reviews and Regulatory Reporting
Timely access reviews are critical for banks to maintain compliance and prevent risky access accumulation. IDHub automates certifications and generates detailed, exportable reports—streamlining FFIEC audits and internal reviews with minimal manual effort.
Role-Based Access for Enhanced Security
IDHub supports role-based access control (RBAC), allowing banks to assign access permissions based on specific job roles. This ensures that employees can only access the data necessary for their responsibilities, reducing the risk of unauthorized access and enhancing compliance. RBAC helps maintain regulatory alignment by ensuring permissions are correctly assigned, updated, and revoked as roles change. By limiting access to sensitive information, banks can improve cybersecurity and minimize exposure to potential data breaches.
Reduce Cybersecurity Risk
Governance and Compliance in Finance
Compliance Risk Maturity
Construct an unified control framework with FFEIC, EU-GDPR, UK-GDPR, SOX, PCI-DSS, BSA, GLBA, PSD 2 compliances to mitigate your threat landscape.
Multi-Factor Authentication
Build an enhanced authentication controls for high risk individuals and other elements with our enterprise-wide approach
Threat and Risk Management
Mitigate risks for applications and physical systems along with customer-permissioned entity's access to your information systems
Cloud Based Inventory
Manage customers, transactional capabilities (e.g. bill payment, wire transfer, loan origination), customer information accessed, and more.
Compliance Tools for Cyber Security
Cyber Security Tools
Cybersecurity Assessment Template
Discover why cybersecurity assessments are vital for regulated industries—plus a free template to strengthen security, manage risk, and stay compliant.

Banking Compliance-Access Reviews & Reporting
Learn how access reviews and reporting protect data, reduce risks, and ensure compliance with regulations like FFIEC, SEC, GDPR, and SOX for financial institutions in our blog post.
5 Access Control Challenges for Finance
Our blog post explain how IDHub simplifies IAM for financial institutions, ensuring regulatory compliance, efficient onboarding, robust security, and reduced IT workload.