What is privileged access management (PAM) and cloud native?
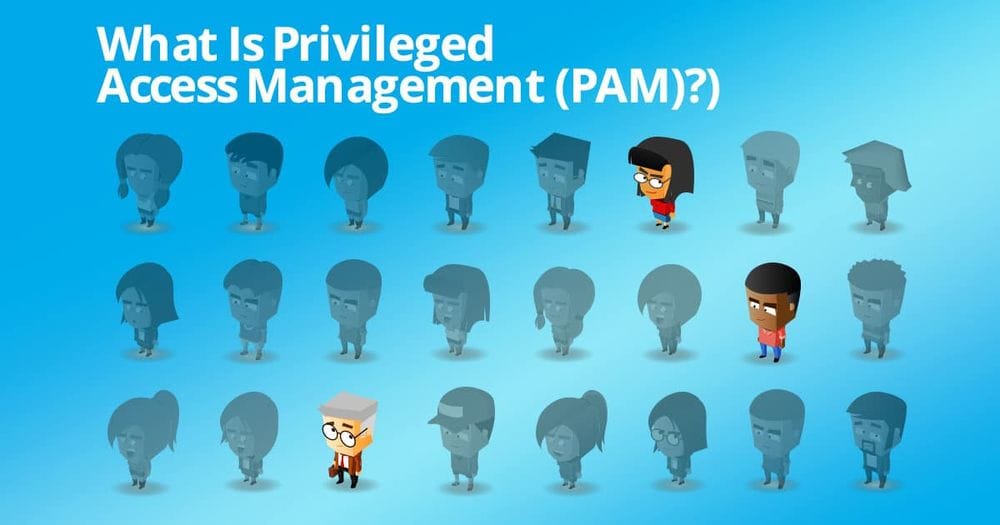
With the widespread adoption of cloud computing, organizations are rethinking how they secure sensitive systems. A key component of modern cybersecurity is Privileged Access Management (PAM). In today’s pam for cloud native environments, managing privileged access control is more complex than ever—demanding secure access, automation, visibility, and scalable pam solutions.
From what is just in time access to privilege elevation and delegation, pam as a service strategies must align with the dynamic nature of the cloud. This blog explores essential PAM concepts, addresses modern challenges like external threats, and outlines best practices and technologies reshaping cloud access management in both human and non-human users scenarios.
Understanding Privileged Access Management (PAM) in the Cloud Native World
As enterprises embrace cloud-native services to drive agility and scalability, their approach to secure access and remote access must evolve. PAM for cloud environments secures administrative admin accounts and privileged accounts to sensitive resources, enabling organizations to mitigate risks—from external threats to insider misuse—and enforce regulatory compliance.
Key capabilities like privilege elevation and delegation management help ensure that privileged users receive elevated access only when necessary. This minimizes standing privileges on both admin accounts and non-human users, improving both compliance and risk posture.
Definition and importance of Privileged Access Management
Privileged Access Management (PAM) protects critical systems by controlling and auditing high-level permissions for both human privileged users and non-human users like service accounts. Without strong privileged access control, misuse of admin accounts and privileged accounts can expose organizations to data breaches, insider threats, and regulatory penalties.
Effective PAM—whether on-premises or delivered as PAM-as-a-Service (PAMaaS)—limits unauthorized access by enforcing least privilege, securing credentials, enabling secure access, and auditing sessions. This is especially vital for DevOps teams deploying applications across multi-cloud pipelines.
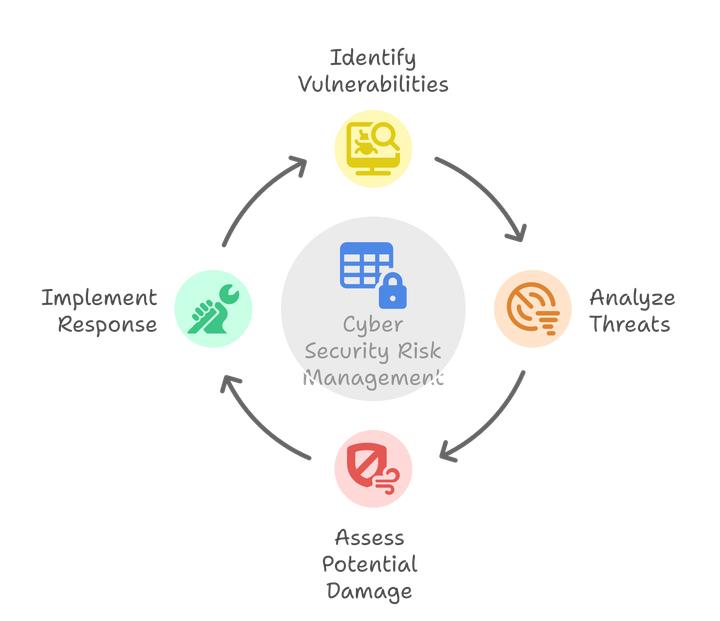
Key Challenges and Security Risks of Privileged Access in Cloud Environments
Implementing Privileged Access Management within a cloud-native ecosystem presents unique challenges and risks. In the cloud, infrastructure and services can be more dynamic, with levels of access changing frequently to adapt to continuous integration and delivery. Here, identity-based attacks have become more prevalent, where attackers target privileged credentials to escalate their access.
The risks associated with privileged access in the cloud include:
- Unauthorized access to critical assets and networks, potentially compromising the entire infrastructural security posture.
- Difficulty in tracking and managing privileged access across different cloud platforms and services.
- Lack of visibility into privileged activities, making it hard to detect privilege misuse or a data breach.
- Challenges in applying multi-factor authentication consistently across all cloud services.
To mitigate these risks, organizations must consider a holistic cloud access management approach to PAM that includes automating privilege access controls, just-in-time privileged access management, automated privileged elevation and delegation management, stringent session management policies, and regular auditing.
This approach will ensure that security teams have greater control and can respond more swiftly to potential security incidents relating to privileged access within their increasingly complex cloud environments.
Integrating Identity and Access Management (IAM) with Cloud-Native PAM
In modern cloud-native environments, Identity and Access Management (IAM) and Privileged Access Management (PAM) work hand-in-hand to deliver a unified access governance framework. By combining IAM’s broad identity lifecycle controls—such as access reviews, reporting, and manager delegation—with PAM’s micro-controls for elevated permissions, organizations achieve both scale and security for all privileged accounts and non-human users.
Key IAM features that enhance your PAM solutions in the cloud include:
Access Requests & Just-In-Time (JIT) Provisioning
Users submit access requests through a self-service portal, and manager delegation workflows automatically approve or deny based on policies. JIT provisioning then grants elevated access rights only for the duration needed, minimizing standing privileges across admin accounts and service identities.
Access Reviews & Certification Campaigns
Scheduled or ad-hoc access reviews validate that privileged users and standard users still require their current access levels. Automated reminders and audit-ready logs ensure your organization meets strict compliance requirements such as GDPR, HIPAA, and SOC 2.
Comprehensive Reporting & Audit Trails
Identity Management reporting dashboards provide real-time visibility into who has access to critical systems and critical resources, while PAM session logs record every privileged session. Together, these reports support forensic analysis, regulatory audits, and proactive threat hunting.
Manager Delegation & Role Management
Empower line-of-business managers to oversee access assignments via delegated IAM consoles. Coupled with role-based access control (RBAC) in PAM, this ensures access governance remains dynamic and aligned with evolving job responsibilities.
Policy-Driven Access Governance
Centralize policies for both IAM and PAM—covering least privilege, multi-factor authentication, and conditional access—to enforce consistent, end-to-end controls across hybrid and multi-cloud platforms.
By tightly integrating IAM capabilities with cloud-native PAM, organizations can automate cloud access management, reduce security risks, and deliver a seamless, compliant identity-to-privilege workflow that adapts to today’s fast-paced DevOps pipelines.
Video - PAM & Cloud Native Panel Discussion
The Role of Privileged Access Management in Cloud Environments
In cloud computing, Privileged Access Management is vital to securing the most sensitive operations. Unlike static on-prem environments, cloud services are dynamic and require granular, real-time privileged access control.
PAM enforces restrictions on who can access admin accounts and critical systems, while session tracking and multi-factor authentication (MFA) enhance accountability and resilience against both external and insider threats.
Overview of Cloud Environments and Their Unique Security Challenges
Cloud environments introduce unique challenges that traditional security models can’t handle:
- Ephemeral resources complicate static access policies.
- Expanded attack surfaces demand continuous monitoring for external threats.
- Cross-platform access increases credential sprawl across privileged accounts.
Security teams must rethink PAM by focusing on visibility, automation, and an identity-first approach to cloud access management, covering both human and non-human users.
Benefits of Implementing Privileged Access Management in the Cloud
Adopting PAM solutions in cloud environments delivers several business-critical benefits:
- Stronger security with enforced least privilege and complete audit trails for admin accounts, privileged users, and non-human users accessing critical systems.
- Improved compliance with regulations such as GDPR, HIPAA, and SOC 2 under regulatory compliance frameworks.
- Operational agility by automating provisioning and revocation of remote access, reducing reliance on manual processes and ensuring consistent enforcement of privileged access control.
- Better visibility into privileged sessions, faster threat detection, and response to external threats and anomalous behavior.
- Secure access is maintained across hybrid and multi-cloud environments, enabling organizations to scale confidently while protecting privileged accounts from compromise.
- Seamless integration with cloud access management tools ensures real-time oversight and reduces security gaps tied to dynamic infrastructure changes.
By aligning PAM with cloud-native principles, businesses gain both protection and performance, while meeting the growing demands of distributed workforces and modern DevOps pipelines.
Best Practices for Privileged Access Management in the Cloud Native World
Securing privileged access in a cloud-native environment requires a robust set of best practices to manage privileged access effectively. With security teams facing sparse boundaries of critical systems and a fluid attack surface, a disciplined approach becomes imperative. Privileged access management should focus on minimizing risks associated with privilege misuse and safeguarding against breaches born out of compromised privileged credentials. Best practices include:
- Principle of Least Privilege: Assign the minimum levels of access required for users to perform their tasks, thereby reducing the potential impact of compromised credentials.
- Regular Audits and Reviews: Periodically review and update privilege requirements to stay aligned with evolving roles and the shifting security posture of the organization.
- Credential Security: Securely manage and rotate privileged credentials, making it harder for attackers to maintain unauthorized access.
- Real-Time Alerts and Response: Implement tools that provide alerts for suspicious activities involving privileged accounts, coupled with rapid response protocols.
Incorporating these strategies fosters a secure cloud environment, aligns with the continuous and iterative nature of DevOps teams, and reinforces the organization's defenses against identity-based attacks.
Adopting a Zero Trust approach to Privileged Access Management
A Zero Trust model is critical for securing privileged user access in today’s cloud-native environments, where traditional perimeters no longer exist. In this model, no user—whether a standard user, super user, or non-human user—is automatically trusted. Every request for remote access, elevated permissions, or access to systems must be verified.
Core Zero Trust best practices for privileged access management include:
- Multi-Factor Authentication (MFA) for all admin accounts, privileged accounts, and critical resources. This adds an essential layer of security against external threats.
- Micro-segmentation to restrict lateral movement and reduce the blast radius of potential breaches.
- Continuous monitoring and behavioral analysis to detect abnormal activity across all user types, including service accounts.
By adopting Zero Trust, organizations strengthen secure access, reduce security risks, and meet growing compliance requirements in the cloud.
Implementing Role-Based Access Control (RBAC) in the cloud
Role-based access control (RBAC) is an effective framework for managing elevated access rights in dynamic cloud environments. It ensures that privileged user access is only granted when appropriate, minimizing risk while meeting regulatory compliance standards.
To implement RBAC effectively:
- Define roles clearly based on job function, ensuring each access level corresponds to business need.
- Strictly enforce role assignments, especially for admin accounts, privileged users, and non-human users accessing sensitive workloads.
- Continuously audit and adapt roles to account for changes in responsibility and evolving threat landscapes.
RBAC operationalizes least privilege by aligning access permissions with responsibilities. This reduces complexity, limits misuse of elevated permissions, and enhances control over critical resources.
Utilizing Multi-Factor Authentication (MFA) for added security in cloud environments
MFA is a non-negotiable layer of security in safeguarding cloud-based systems. The pivotal elements of utilizing MFA in cloud environments entail:
- Diverse authentication methods: Combine something the user knows (password), something they have (security token), and something they are (bio-metric verification).
- Enforcement policies: Mandate MFA for all users, especially for those accessing sensitive data or critical infrastructure.
- Integration ease: Utilize cloud services that natively support or seamlessly integrate with MFA solutions.
Through the enforcement of MFA, organizations drastically improve their security stance by adding depth to their defense strategy against unauthorized access.
Implementing session recording and monitoring for privileged sessions in the cloud
Session recording and monitoring are essential to overseeing elevated access rights in cloud environments.
Best practices include:
- Comprehensive recording of all privileged user and admin account activities to maintain a complete audit trail.
- Real-time monitoring of sessions to detect and respond to external threats or insider misuse.
- Implementing alerting systems and searchable logs to enable rapid investigation of suspicious activity.
These controls not only support incident response and accountability but also help organizations meet strict compliance requirements around privileged access control.
Leveraging Identity-Native Infrastructure Access for better security control
In a cloud native environment, identity native infrastructure access places identity—not the network—as the foundation of privileged access management.
Key implementation practices include:
- Verifying user identity through trusted sources before granting elevated permissions.
- Enforcing conditional access policies that adjust dynamically based on context and real-time risk signals.
- Integrating identity controls directly with DevOps workflows to protect access for both human and non-human users.
This model enhances cloud access management by tying privileged user access to verified identities, thus securing critical resources and meeting stringent compliance requirements.
Video - PAM & Cloud Native Panel Discussion
Cloud Native Privileged Access Management Solutions
Cloud Native Privileged Access Management (PAM) Solutions are pivotal in mitigating risks associated with privileged access within modern cloud infrastructures. The proliferation of cloud services has expanded the potential attack surface, making traditional security paradigms inadequate.
Adaptive PAM solutions now play a crucial role in controlling and monitoring privileged user actions, providing a vital layer of security across distributed systems. These solutions are designed to operate natively in the cloud, enabling streamlined integration with cloud services, enhanced scalability, and consistent enforcement of privilege access controls.
Evaluating features and capabilities of Cloud-Native PAM solutions
When evaluating cloud-native PAM solutions, key features and capabilities to consider include:
- Scalability: The solution should easily scale up or down with the dynamic needs of the cloud environment.
- Session Management: Must include privileged session recording, session monitoring, and the ability to terminate sessions proactively.
- Compliance: The ability to enforce policies that comply with regulatory standards such as GDPR, HIPAA, or SOC 2.
- Integration: Seamless integration with existing cloud services, CI/CD pipelines, and DevOps workflows.
- User Experience: Solutions should enable security without hindering user productivity, offering a balance of security and accessibility.
- Visibility and Reporting: Comprehensive dashboards and reporting capabilities for audit and compliance purposes.
Considering these factors ensures that organizations choose a PAM solution that not only fits their security requirements but also aligns with their operational dynamics.
Check out our panel discussion to listen to cybersecurity experts discuss PAM and Cloud Native.
Real-world examples of organizations securing their privileged access in the cloud
Organizations across industries are leveraging cloud-native Privileged Access Management (PAM) solutions to reduce security risks, meet compliance requirements, and control elevated access rights. Examples include:
Global Financial Services Firm
- Deployed a cloud-native PAM solution across a multi-cloud infrastructure.
- Integrated multi-factor authentication (MFA), session recording, and privileged session monitoring.
- Strengthened control over privileged users, admin accounts, and non-human users, minimizing external threats.
Healthcare Provider
- Adopted PAM to enforce HIPAA compliance by applying role-based access control (RBAC).
- Monitored access to critical resources like patient records via audit trails and real-time alerts.
- Limited privileged user access and super user privileges to only those with valid operational need.
SaaS Company with Remote DevOps Teams
- Implemented PAM as a Service to manage secure access for developers and third-party vendors.
- Enabled Just-In-Time access, conditional access policies, and continuous privileged access control.
- Ensured proper governance of elevated permissions while aligning with industry compliance standards.
These examples highlight how tailored PAM strategies protect against privileged credential misuse, reduce attack surfaces, and ensure only the right users access the right systems at the right time.
Emerging Technologies and Solutions for Privileged Access Management in the Cloud
As organizations adopt more cloud services and face growing external threats, the evolution of Privileged Access Management (PAM) is critical to maintaining secure, compliant, and scalable environments. Next-generation PAM solutions are integrating advanced technologies to keep pace with dynamic cloud-native architectures and meet rigorous compliance requirements.
Innovations such as AI-driven privileged user behavior monitoring, cloud access management, and PAM-as-a-Service (PAMaaS) are changing how organizations protect elevated access rights, whether for admin accounts, super users, or non-human users. These technologies help mitigate security risks associated with privileged accounts and support effective privileged user access control.
| Technology/Application | Purpose/Outcome |
| AI and ML Enhancements | Predictive threat detection and behavioral analysis |
| Behavioral Biometrics | Continuous verification during privileged access |
| PAM-as-a-Service (PAMaaS) | Simplified management and deployment of PAM solutions |
| Blockchain in Session Management | Immutable session logging for increased accountability |
| Cloud Native Access Controls | Real-time adjusting access controls based on context |
| Session Recording and Analytics | Enhanced real-time surveillance and compliance assistance |
These cutting-edge capabilities support better visibility, reduced privileged credential misuse, and proactive threat response. They also reinforce least privilege strategies and provide flexible, scalable access to systems across hybrid and multi-cloud environments.
By embracing these innovations, organizations can strengthen privileged access control, streamline compliance audits, and ensure robust protection of critical resources against evolving cloud security challenges.
Securing the Future of Privileged Access Management in Cloud-Native Environments
As cloud-native infrastructures evolve, organizations must align Privileged Access Management (PAM) with broader Identity and Access Management (IAM) strategies. IAM delivers essential capabilities—like access reviews, just-in-time provisioning, manager delegation, and audit-ready reporting—that complement PAM’s focus on privileged user access, elevated permissions, and secure session management.
Together, IAM and PAM create a layered, identity-centric defense that secures admin accounts, non-human users, and critical cloud resources while meeting complex regulatory compliance needs. By adopting integrated, cloud-native PAM solutions enriched by IAM best practices, organizations gain the agility, scalability, and visibility required to mitigate external threats and protect access across today’s dynamic environments.