Identity And Access Management Compliance

IAM Access Reviews
IAM systems are excellent at providing an insight into who has access to what within your organization.
However, If no one is paying attention, all of that security could be going to waste.
For businesses to take full advantage of their Identity Management system, they should have a process to review all employee access and permissions at any given time.
The best way to maintain your system's security is to periodically audit the user access to all applications, networks, documents, and any other asset your organization may use.
Additionally, some industries have mandatory regulatory compliance rules, requiring administrators to certify users and applications, to prove compliance, on a scheduled basis.
Identity and Access Management (IAM) systems use this certification process to validate user access to organizational resources, or to revoke access as needed.
Regulations vary across industries, such as HIPAA in healthcare, FISMA in U.S. federal agencies, or PCI-DSS in retail and financial services.
Without an efficient IAM solution in place, with a centralized identity directory, certifying user access privileges can be a daunting process for administrators.
Regardless of potential regulatory issues, compliance controls through access certifications help organizations ensure internal security standards are met, by verifying employee access, to the resources needed for proactive enforcement of their internal access control policy.

Access Certification Process
Change within an organization happens constantly.
Throughout an employee's lifecycle with a company, they are likely to change roles, departments, locations, take on new responsibilities, or use different applications.
The possibility a former or transferred employee has access to systems or unsuitable permissions within it, is a security risk and a daily concern for most organizations.
When change happens, or when a request is submitted to certify a user or application, a certification request is generated to verify (certify) the employee's access is correct.
Or, to certify an entire application's user base and role assignments, ensuring there is not any inappropriate access granted.
A reviewer, or certifier, will examine the user or application, through various manual or automated processes, to determine if the user or users have the appropriate access, and then complete the certification.
User Access Review
Certifying a user's access to all of their applications is not as common as certifying which users have access to a specific application(s), but there are still times when this is needed.
If a user changes their department, role, or even office location, the new location or management team may want to review all of his/her current access, ensuring he/she has access to only what is needed.
Additionally, restricted rights within a user's previous role, may no longer be valid in their new position, causing an Identity risk.
Another reason to certify access by user, may be due to a change in management. If a new department manager wants to ensure their department runs efficiently, conducting a thorough audit is an excellent first step.
One last possibility for a certification, could be due to the occasional extended leave of absence by managers, application owners or even a single user.
For example, during an extended absence, an employer may want to review and limit the user's account access, while not using it until they return.
In the case of a User Access Review, the certifier would obtain a complete list of all resources the user has access to, along with any entitlements or permissions granted to the user, within those applications.
During the certification process, the certifier would review every item, or outsource it to another reviewer or manager.
Security Managers and Application admins may have better knowledge and understanding of the user’s access rights, ensuring the accuracy of access reviews.

Application Access Review
In addition to conducting reviews for business users, access certification reviews can also be based on the application or resource.
During an application review a specific resource, or a collection of resources, and audit who has access to them, and at what level.
Resources can be applications, entitlements, roles, or any other asset an organization uses.
In many cases, requests to certify an entire user base for a specific application, will be part of required compliance regulations.
Additionally, timely certifications may be an excellent internal business practice for applications, allowing access to highly sensitive information.
Access Certification Campaigns
On many occasions, it can be a much more involved project to try and conduct large scheduled application audits, groups of applications, or multiple users at the same time.
Scheduling and creating periodic and necessary access review campaigns involve using a large dataset to perform multiple certifications simultaneously.
Conducting frequent reviews by security managers with detailed instructions as part of your access control operational standards can help to reduce business risk.
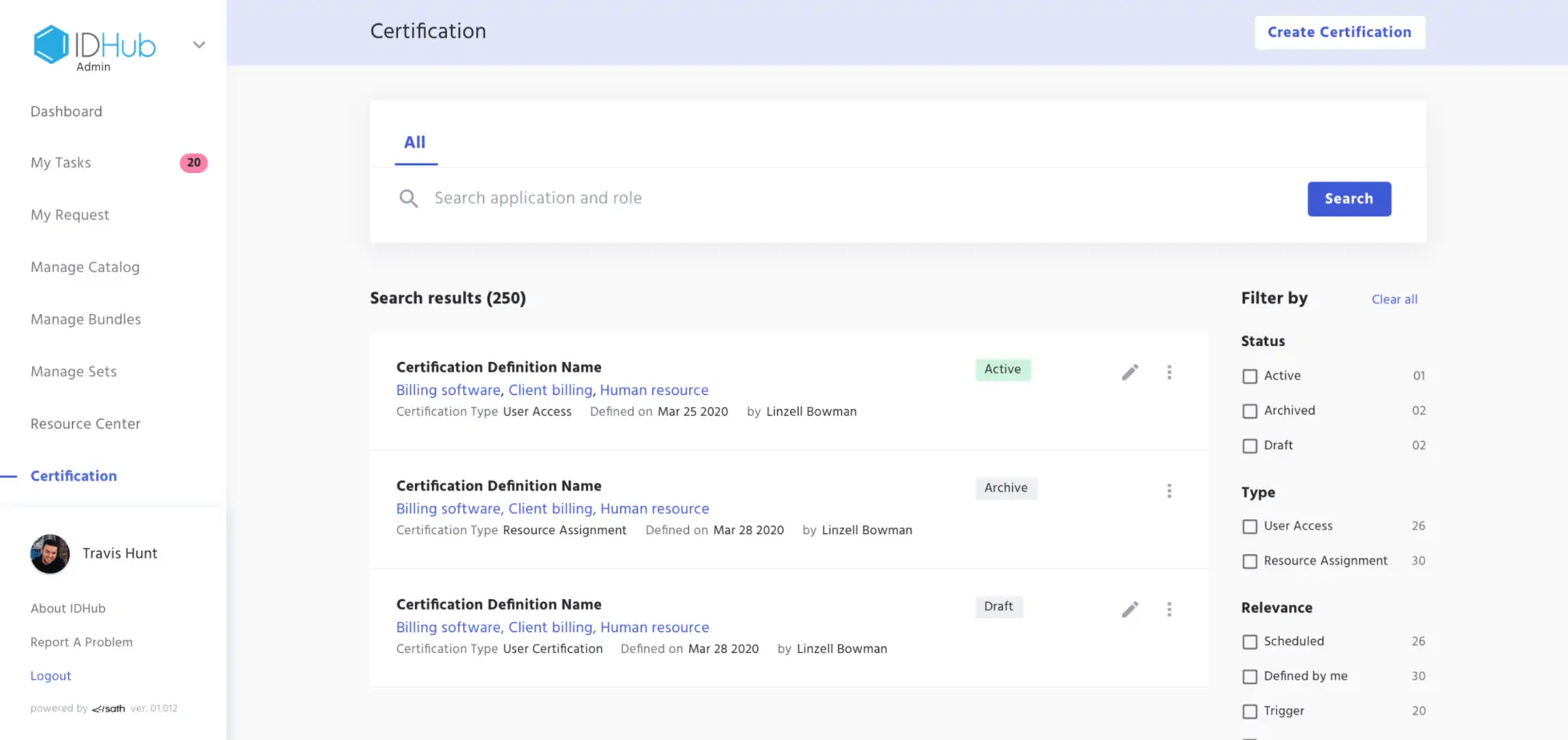
Access Reviews in IDHub
IAM Access Reviews are simple and efficient in IDHub with a feature called Certifications.
Certifications are created and managed by IDHub administrators.
- Modify existing Certification definitions
- Run definitions in real-time
- Schedule a definition to run at a later date and time
- Archive an old Certification definition that is no longer in use
- Maintain security policies to prevent unauthorized access
- Conduct automatic Access Remediation
Learn everything there is to know about IDHub Certification Access Reviews.