Secure Remote Workers: 16 Tips To Work Safely At Home
Secure Remote Workers Tips
GET MY COPY
Businesses Still Struggle To Secure Remote Workers.
The sudden shift to remote work during the early weeks of Covid-19 was a difficult adjustment for many organizations.
Almost two-thirds of businesses had to transition over half of their workforce overnight. In addition, less than half of organizations had a business continuity plan before the pandemic.
This rapid shift to remote work affected everything from basic connectivity to critical business applications. The entire process made basic operations a formidable challenge.
In response to the pandemic, many organizations scrambled to find "good enough" solutions, a fact not lost on would-be hackers (more on that in a bit).
Companies invested further in remote work solutions. For example, 40% of businesses spent more on skilled IT workers to support the now remote IT staff to troubleshoot issues, enable security, and ensure productivity for employees working from home.
The pandemic normalized remote work for many organizations which had very limited or no telecommuting as policy previously.
Many organizations faced severe difficulties in the transition. Nevertheless, they generally found that they could provide employees with the necessary resources and maintain near-fully remote successful businesses.
However, the new work environment brought new challenges and threats.
As a result of the mass transition and the resulting cost-benefit analysis, many companies are planning to allow more remote work indefinitely. Over 50% of employers plan to permanently expand or increase flexible work arrangements. Only 15% of companies report not planning to revisit remote work options post-COVID-19.
What Are The Most Significant Security Risks For Remote Employees?
Phishing
Phishing is a cyberattack used to acquire sensitive information or data from individuals or organizations.
Phishing attacks launch through fake websites, emails, or attachments that appear to be from a legitimate source. But are malicious attempts to gain access to confidential information. This attack is particularly hazardous to remote employees due to their lack of direct contact with their employers and tech staff.
Phishing attacks can have severe consequences for individuals and organizations as they are usually the first entry point to much more severe infiltration.
Phishing attacks can lead to severe financial losses and data breaches and damage an organization's reputation costing far more in the long run.
Weak Password Security
Oddly enough, weak password security is still a significant security risk for remote employees due to a lack of single sign-on solutions or two-factor authentication and often relying on user-generated passwords rather than, at a minimum, using sophisticated password managers.
As most people know, malicious actors can easily exploit weak or duplicate passwords. For example, if an employee reuses a weak password across multiple accounts, a breach on one of those accounts will expose all of the employee's data.
Additionally, if a hacker compromises an employee's personal account, they will use that password to access the work accounts, leading to a devastating breach.
Unmanaged Personal Devices And Remote Access
One of the remote staff's most significant security risks is using improperly patched or outdated software on personal devices to access work resources.
When unmanaged devices are compromised, they open up new vulnerabilities across the network.
Relying on users to maintain proactive best practice security protocols on their devices has frequently led to ransomware attacks and other security breaches on business networks.
Ultimately, the best practice for remote employee security is to provide managed company devices or office computers that are correctly updated and secured and have clear policies to govern how employees work remotely and how they protect the equipment at their homes.
Unsecured Direct Access To Cloud And SaaS Apps
The security risks associated with unsecured cloud and SaaS app access for remote employees add to the potential for breaches.
The lack of oversight by IT staff can result in unauthorized access to corporate data.
The risks of malware and malicious attacks multiply when users use non-company equipment to access internal resources.
Hackers Saw Remote Work As An Opportunity
When cyber attackers saw the rapid shift to remote work, they recognized the chance to exploit the increased use of personal devices.
Hackers knew that the attack surface had greatly expanded and weakened simultaneously.
Phishing attacks compromised businesses through email schemes, ransomware, and even nation-state-backed campaigns. All hacking types saw a massive surge in activity due to the increased vulnerability of remote workers and their endpoints.
This sharp increase in attacks was elevated even further by remote IT staff and the use of less-than-optimal technology.
As a result, organizations had to rush to find new and secure ways to connect, maintain, and secure access to business-critical resources.
How To Address Remote Work Security Challenges?
Step 1: Develop a documented work-from-home security policy that outlines acceptable use and security measures that all employees should follow.
Step 2: Restrict business operations to business devices or Implement a Bring-Your-Own-Device (BYOD) policy, as many employees may use their personal devices to access company systems and data. This policy should include how to securely register and maintain machines and which software and networks employees may use.
Step 3: Provide cyber security awareness training and tips to employees (Such as the PDF download below) to ensure that they understand the risks associated with working remotely and know how to protect themselves from potential threats.
Step 4: Use a secure video teleconferencing platform that provides end-to-end encryption, such as Zoom, Microsoft Teams, or WebEx.
Step 5: Invest in a centralized storage solution, such as a cloud storage system, and encourage staff to back up data regularly.
Step 6: Use up-to-date, secure antivirus and anti-malware software to detect and remove malicious programs.
Step 7: Utilize Single Sign-on, or at a minimum, password managers with two-factor authentication when accessing company systems and data.
What Are Remote Work Security Best Business Practices To Reduce Risks?
- Establish Identity Access Management (IAM) & Multi-Factor Authentication (MFA): IAM platforms are essential for effectively managing and monitoring secure access to corporate systems and data, regardless of the user's location.
- Require Multi-factor authentication whenever users sign in to a corporate system.
- Implement Encryption Strategies: Encrypting data helps organizations protect their information at all times, including when it moves beyond the corporate network.
- Manage Endpoints: Security teams must ensure they have proper visibility and oversight of the various devices employees use when working from home and other remote locations.
- Require that personal devices comply with corporate security protocols.
- Monitor and Test: Monitoring environments for unusual activity and other signs of potential threats can prevent or stop a security breach before too much damage is done.
- Regular testing of systems for potential vulnerabilities is also beneficial.
- Use Corporate Email Solutions - Require employees to use corporate email solutions to store or transmit personal data rather than rely on their messaging accounts.
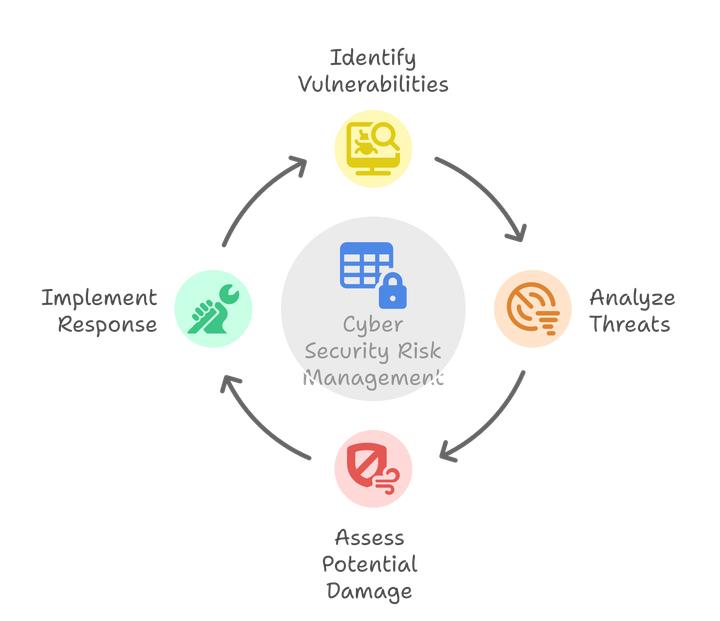
- Regularly conduct third-party risk assessments - Contract a third-party security partner to assess vulnerabilities. Risk assessments can identify company system and procedure weaknesses using the same processes a hacker would to breach the system.
Cyber Education Is Critical
Cybersecurity threats are on the rise due to a variety of factors. However, more remote workers and personal devices may be the most significant factor.
In Cybersecurity, employees are the first line of defense and also the weakest.
Organizations must ensure their remote workers receive proper cyber security training and education to mitigate the high risk of human error, negligence, ignorance, and susceptibility to schemes.
Security training should include:
- A review of the company's policies.
- Details about the methods and processes it contains.
- Recognizing phishing emails
- Properly using secure network connections.
- General Security Practices
Additionally, remind workers of the risks of using simple passwords.
Cyber education is vital to protecting organizations, as employees are the most common entry point.
Tips For Remote Work From Home Users
- Never log in to a website from an email link.
- Never leave office devices unattended.
- Avoid personal browsing on office devices.
- Keep personal information hidden during video meetings.
- Hide your home WiFi network by turning off the broadcast setting.
Read the complete list of 16 tips with additional details on each by downloading the printable PDF file to share with your team.
Steps To Protect Data In Remote Work Environments
Steps to Protect Data in Remote Work Environments:
- Implement Disk Encryption: All endpoints should be protected with full disk encryption to prevent sensitive data from being read from the memory of a misplaced device.
- Utilize Data Loss Prevention (DLP): All emails and messages on collaboration apps should be scanned for sensitive data to ensure that it is not leaked to an unauthorized party.
- Implement File Classification: Automated scanning of files for sensitive content should be employed to ensure that data can be appropriately marked and secured.
Enterprises Must Adapt To Long-Term Changes To Secure Remote Workers
Step 1: Begin by investing in security solutions designed to provide the flexibility and scalability needed to secure remote work.
Step 2: Develop and implement a comprehensive business continuity plan to address potential emergency scenarios.
Step 3: Ensure that the IT team is prepared to respond quickly to changes and scale up to ensure business continuity.
Step 4: Plan for a hybrid IT infrastructure that includes on-premises networks, co-location environments, and public and private clouds.
Step 5: Utilize a security-driven networking approach that converges networking and security to protect the enterprise at every edge, from network to cloud.
Step 6: Monitor the remote workforce and update security protocols as needed.
By following these steps, enterprises can adapt to secure remote work for the long term. Investing in the necessary tools and protocols to ensure remote workers' safety and security and the data they access is important.