Setup Multiple ways to do SSO
Page Background: In this document we would discuss the saml method of configuring the SSO.
There are various methods of configuring the SSO, such as: SAML, OpenID Connect, GitHub etc. In this document we would focus on the SAML method of configuring the SSO.
SAML Method of Configuring SSO
The first step is to log into your KeyCloak. For logging into KeyCloak:-
- Login into your IDHub tenant
- Make sure that you have admin credentials to log into your IDHub tenant
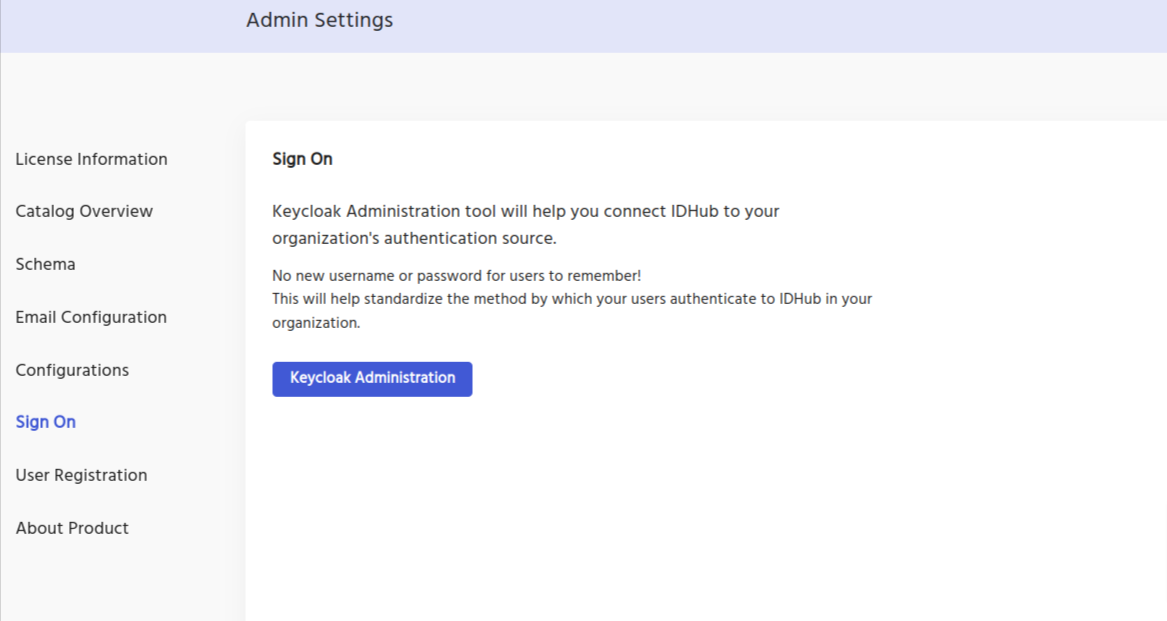
- Click on the
Admin Settingfrom the IDHub dashboard, - Click on
Sign On
Click on the KeyCloak Administration button, and then you will be redirected to your KeyCloak instance.
Creating the SAML client in KeyCloak
The first step is to create a client in your KeyCloak realm. In order to do so:
- Click on the
Clientslink in the left navigation bar in your KeyCloak Realm. - Click on the
Create Clientbutton.
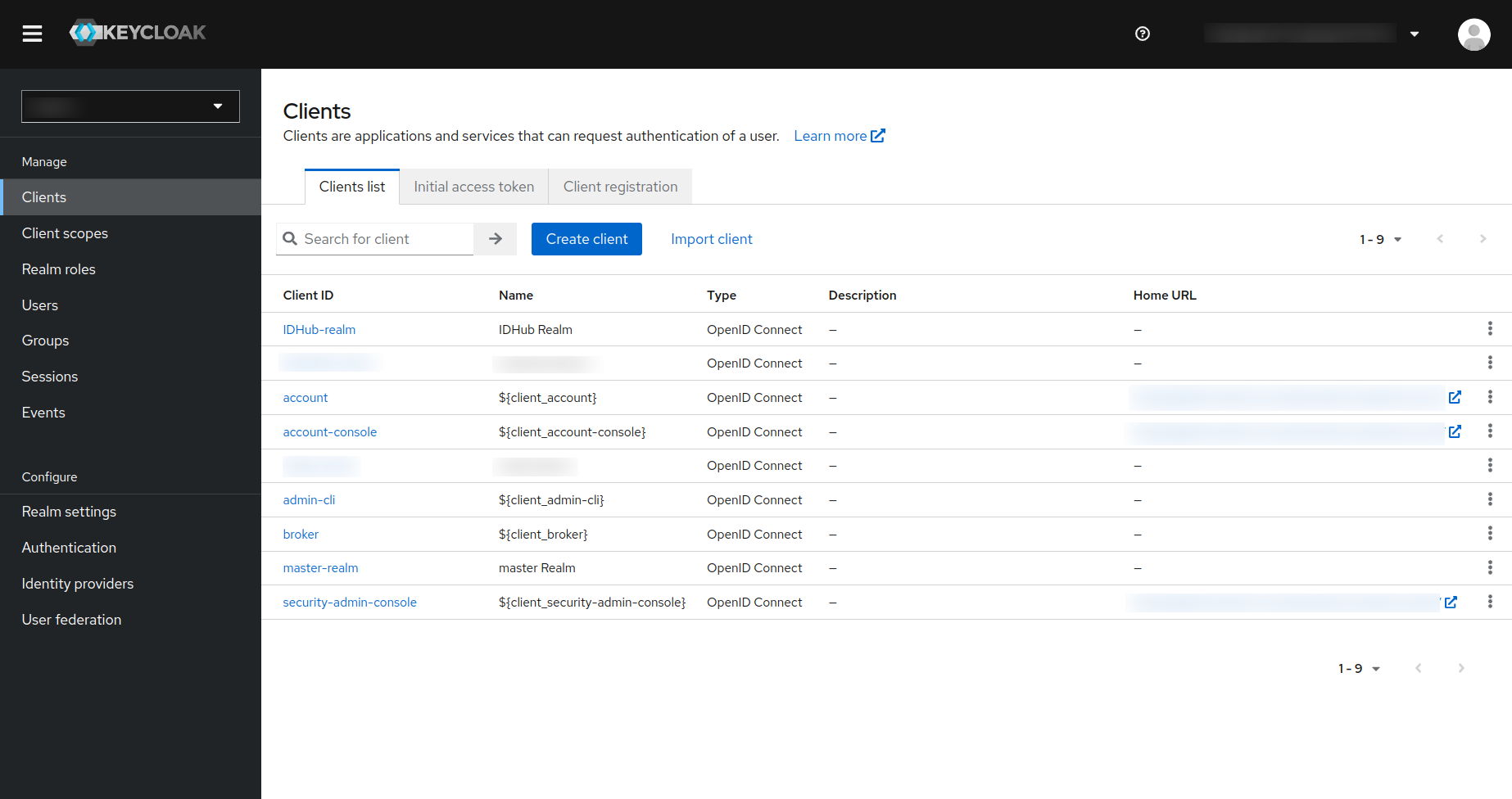
Then you will be taken to the following page:
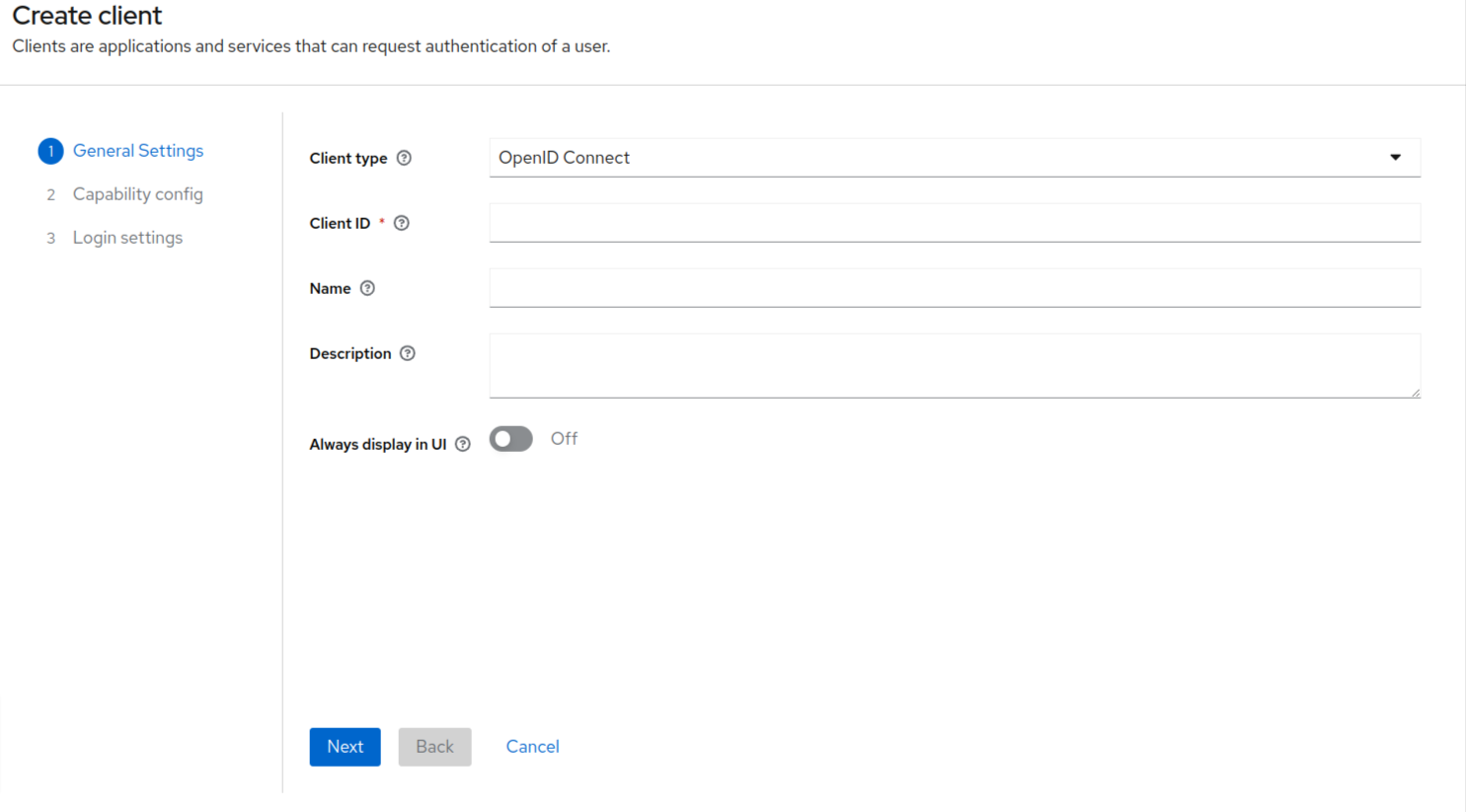
- You need to select the SAML from the Client Type drop-down.
- Since we are going to use the SAML method of setting up the SSO, therefore the client type should be SAML here.
- Enter Client ID and name.
- Click on the next button at the bottom.
This is last step of creating the client.
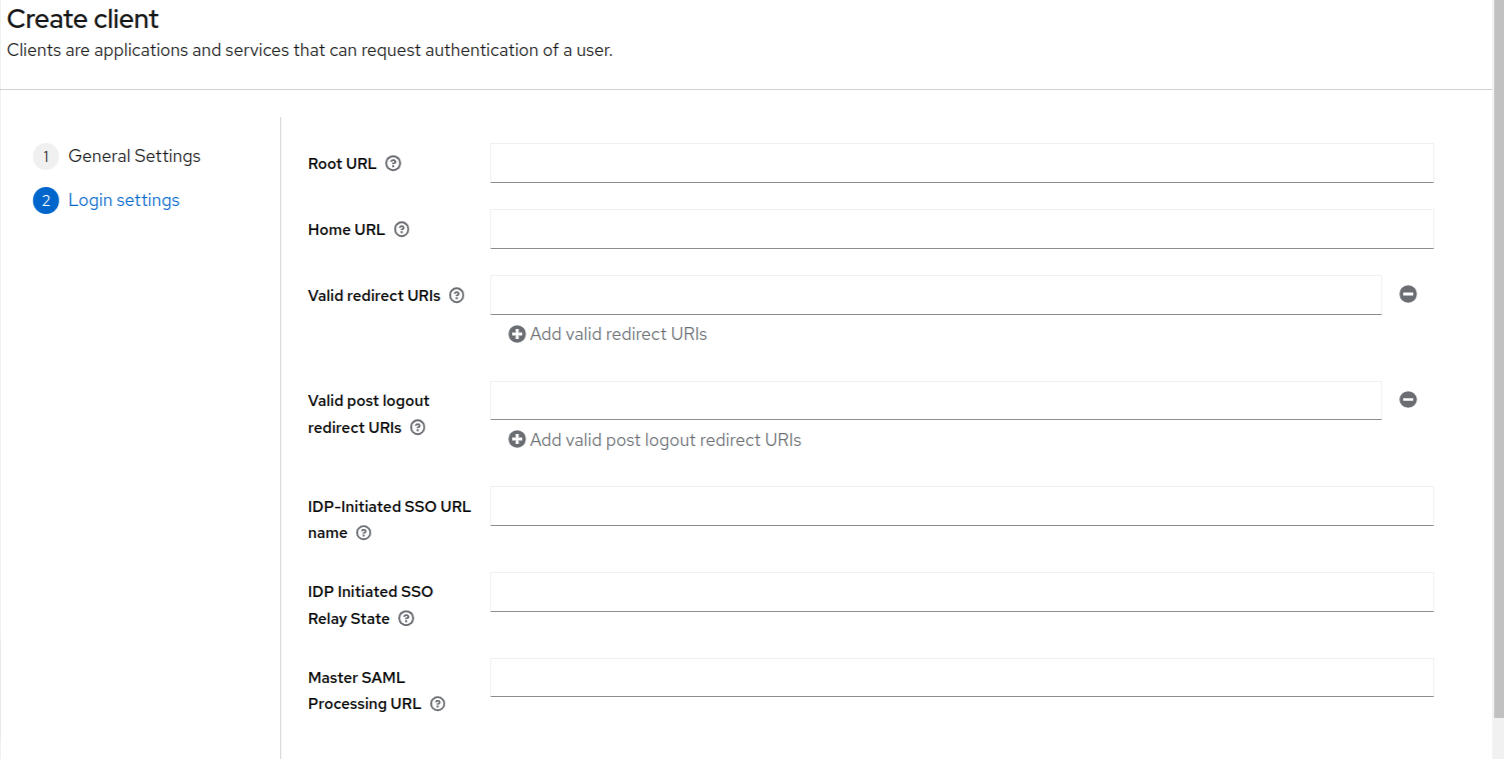
In this page, all the fields are non-mandatory fields. You can just set valid redirect URIs to be “*” and click on the save button at the bottom of the page to create the client.
Creating the First Login Flow
Why do you need itAn authentication flow needs to be configured in KeyCloak. In this tutorial we have described a specific flow which is applicable in scenarios where you do not need to implement additional checks before executing the single sign-on.
However, there can be alternate flows as well, which you can configure in KeyCloak as per your organizational internal policies. For detailed instructions on the KeyCloak authentication, you can refer their offical documentation here
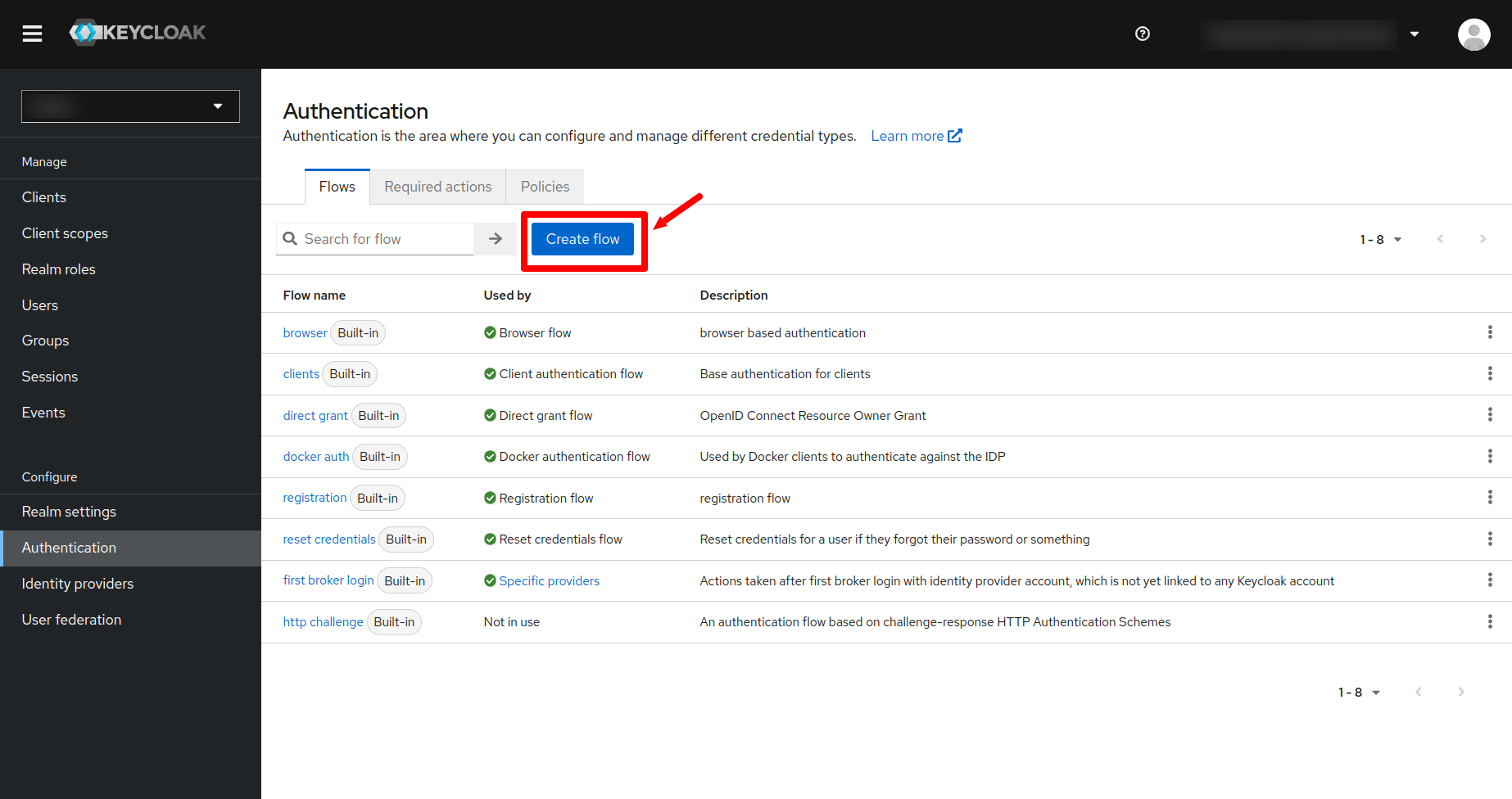
Click on the Authentication menu on the left side navigation bar of the KeyCloak and then click on the create flow button.
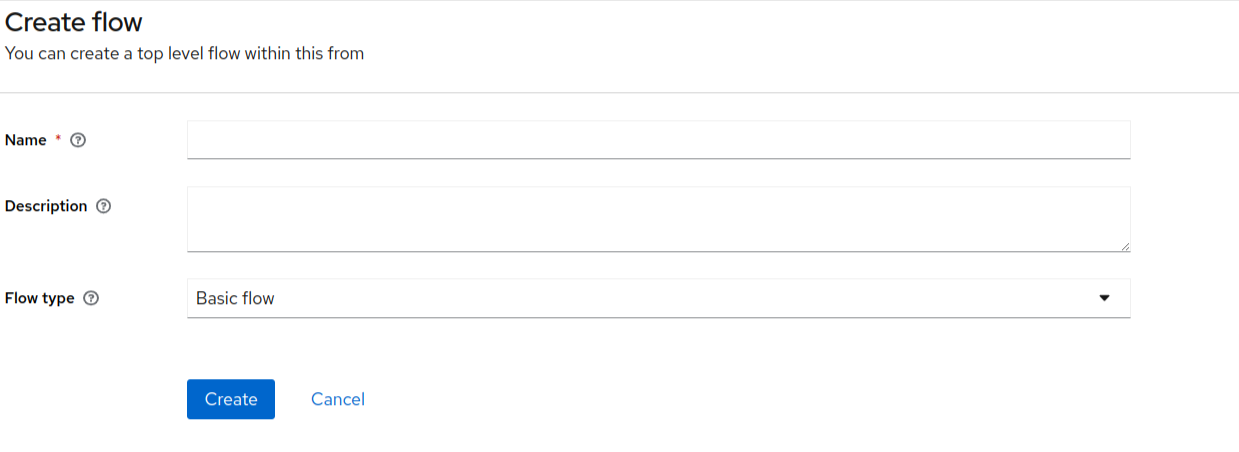
Enter the name of the flow and click on the create button.
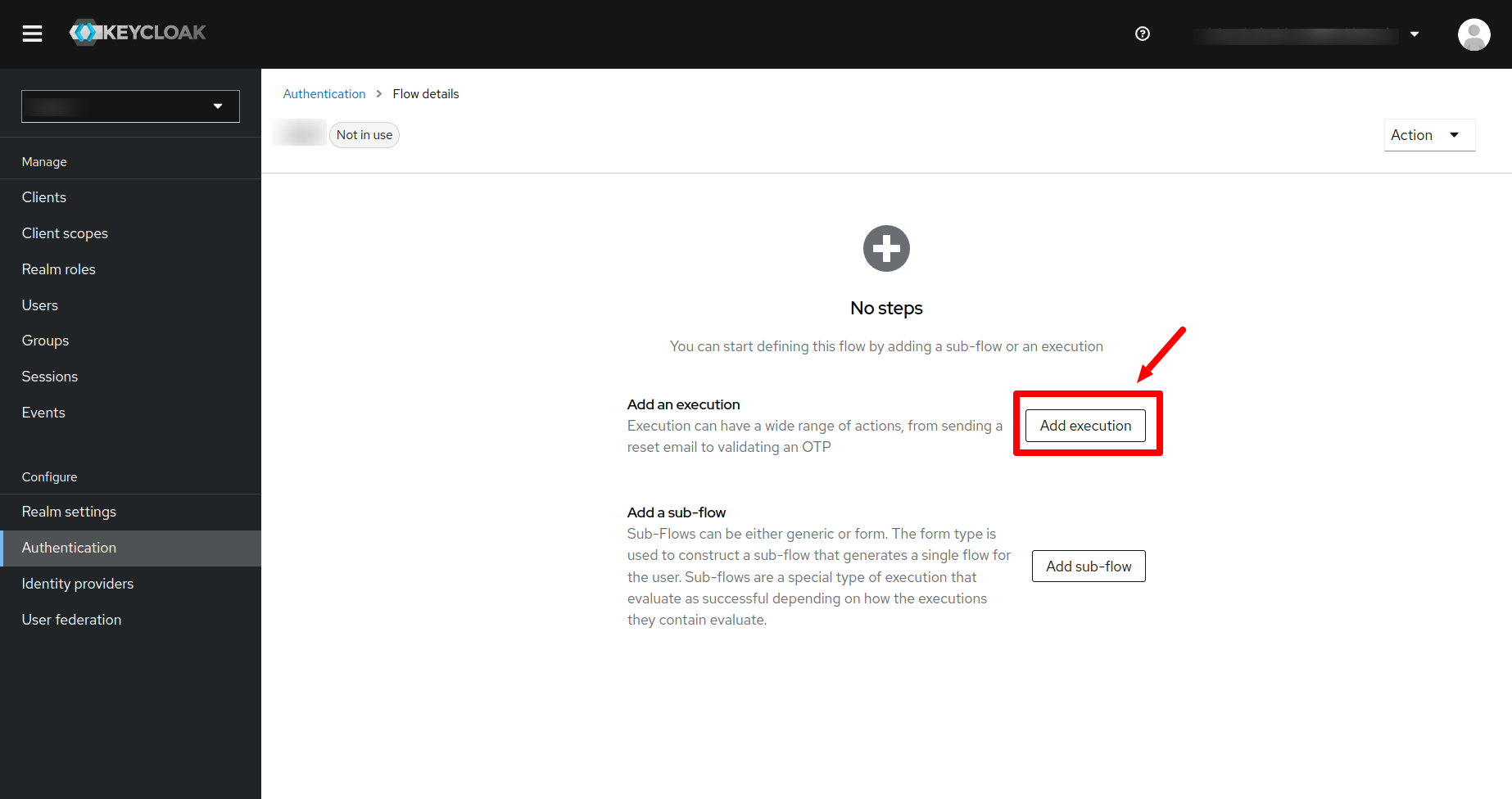
In the next page click on the Add Execution button.
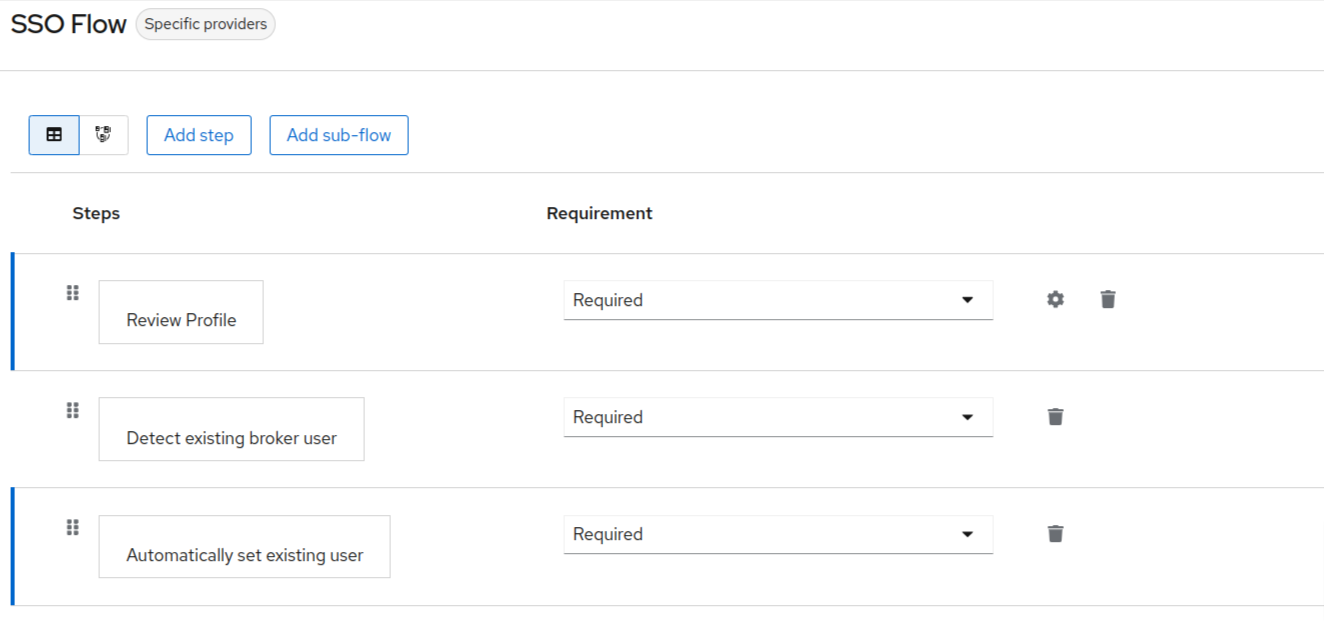
Search for Review Profile and click on the add button. Then you will see the following:
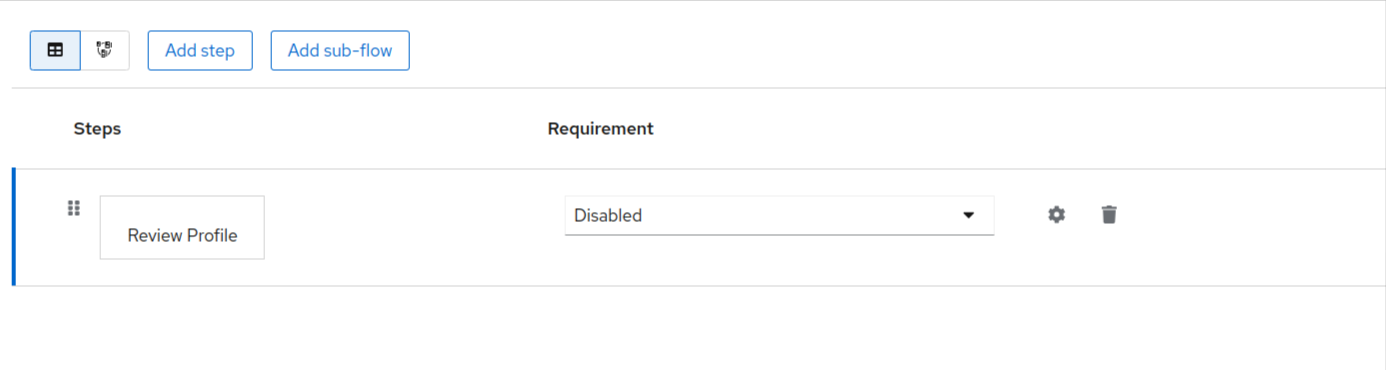
Under the requirement header, click on the dropdown and make that as required.
Repeating the above steps, add the following executions to the flow:
- Detect existing broker user
- Automatically set existing user.
The final executions for the flow would look something like this:
Creating the Identity provider in KeyCloak.
The next step is to create the identity provider in KeyCloak. In order to do so:
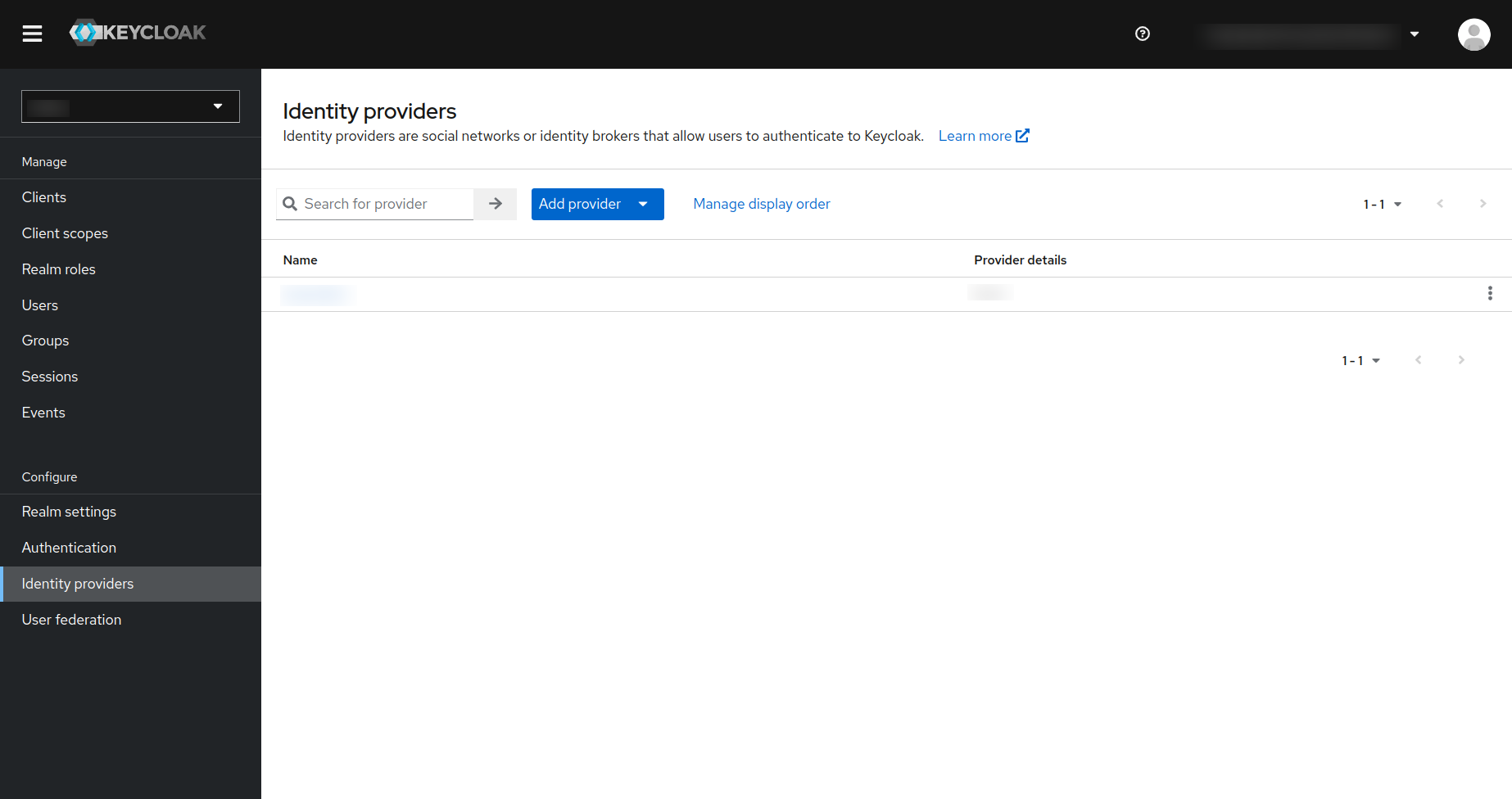
- Click on the
Identity providerin the left navigation menu in the keyCloak and you will be redirected to the following page. - In that page click on the
Add Providerbutton as is shown in the screenshot below:
In the drop-down that is displayed you need to click on the SAML 2.0 option. This will display the following page for adding the SAML provider.
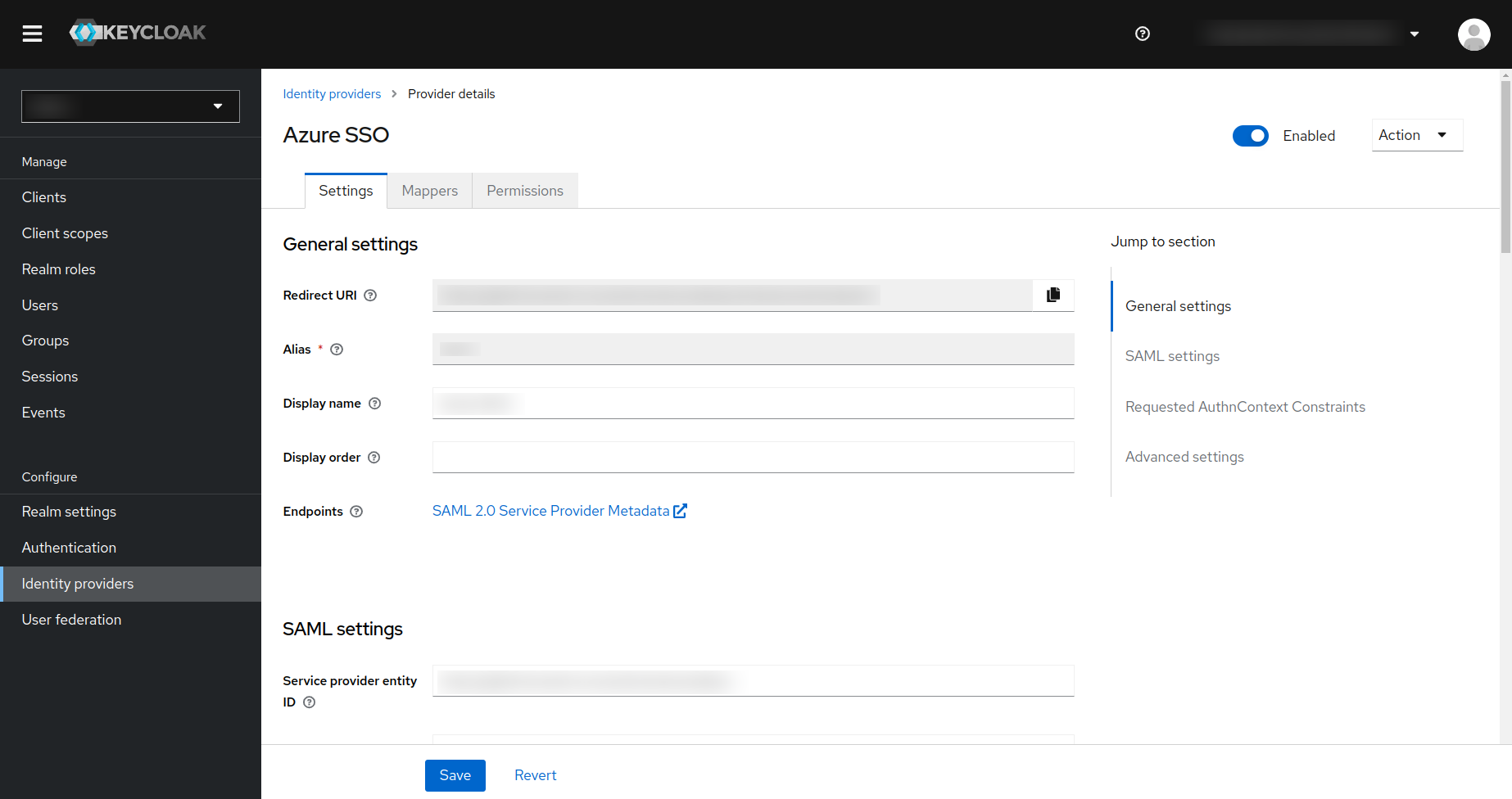
Actions that you need to do- Copy the Redirect URI and Service provider entity ID and keep it somewhere safe as this will be required when configuring your external identity provider.
- Under the
SAML entity descriptor, you need to enter the User Federation Metadata URL from your external identity provider. Consult the documentation for your external IDP for the same. - Make sure that you select the
First Loginflow (which you have created in the previous step) for the identity provider.
Creating the mappers for the Identity provider in the Keycloak.
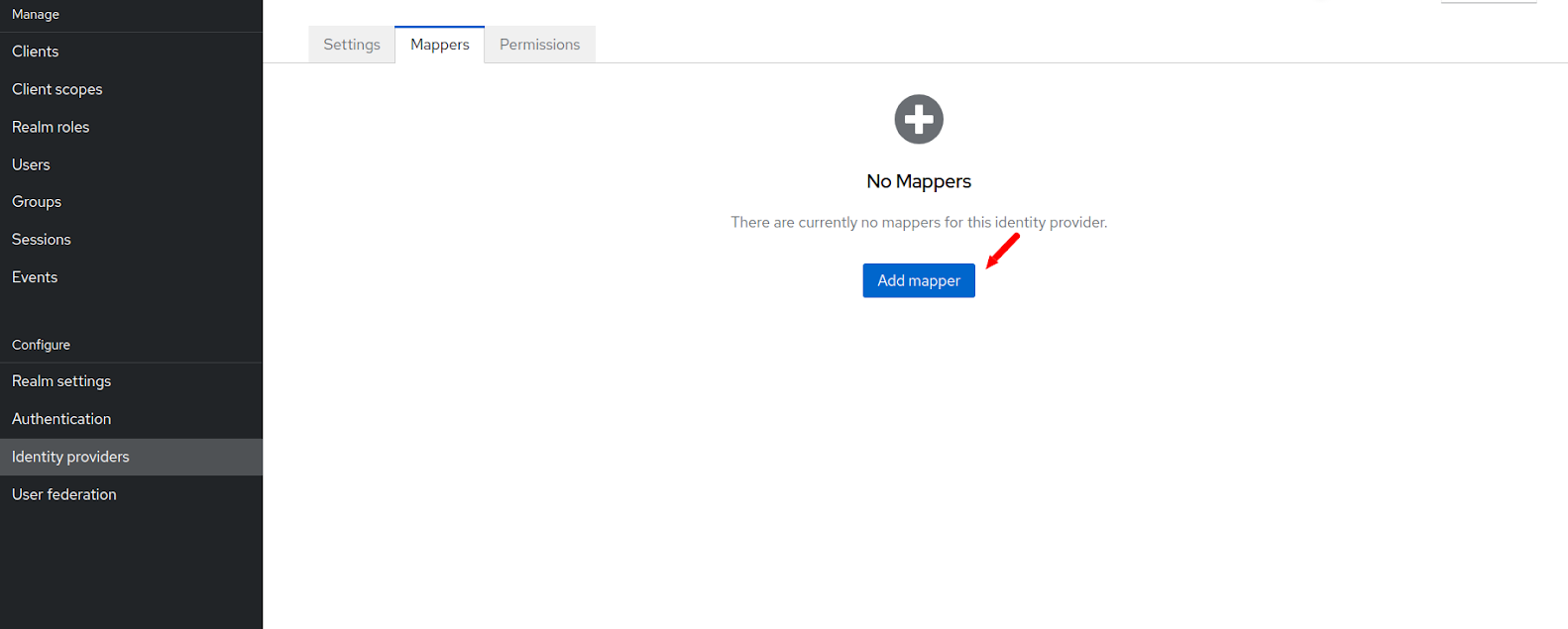
Click on the identity provider link on the left side navigation menu of the KeyCloak and then click on the identity provider that you created in the previous step. Now click on the mapper tab there.
Then click on the Add Mapper button.
In the next page you have to enter the mappers for the email address.
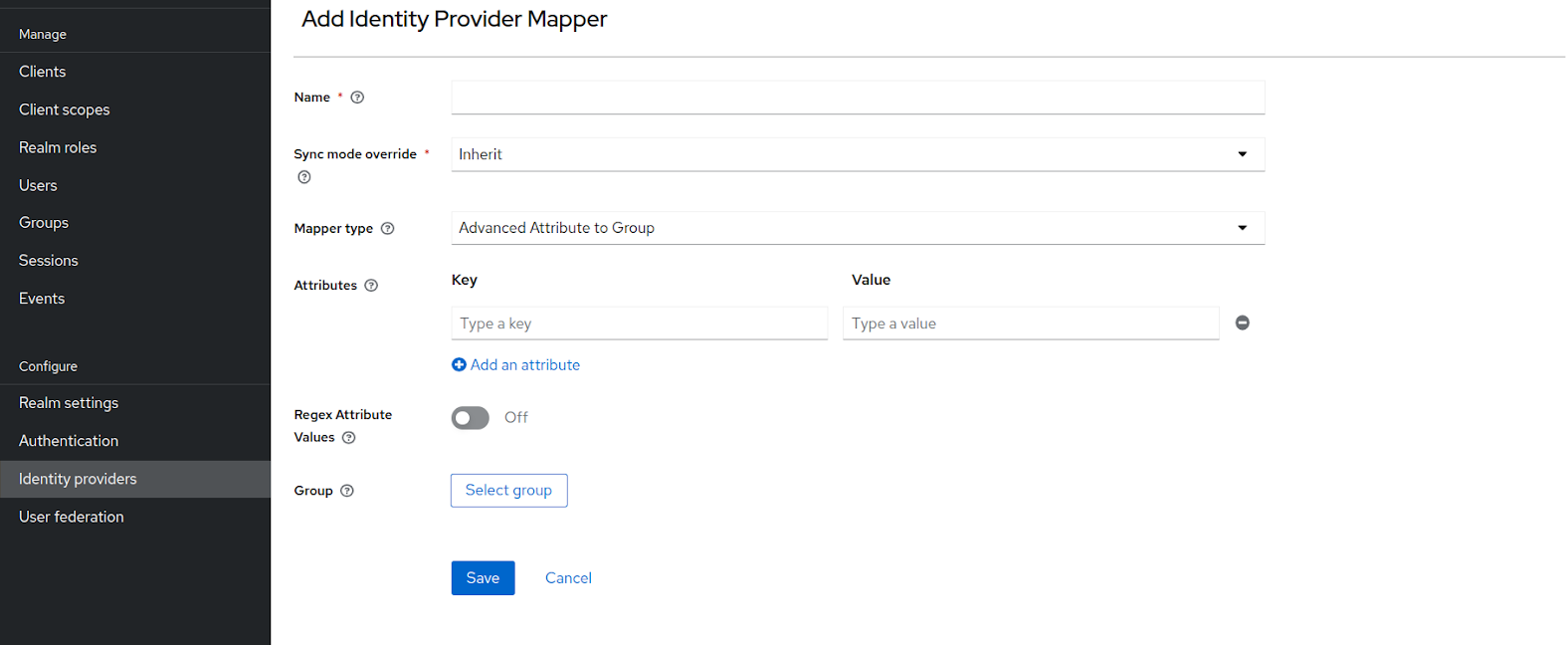
Enter the name of the mapper and then in the sync mode override drop-down select import.
Under the mapper type, select “Attribute importer”. Although non-mandatory, you can also enter the attribute name and user attribute name.
After entering the required information, hit the save button. The final mapper can look something like this:
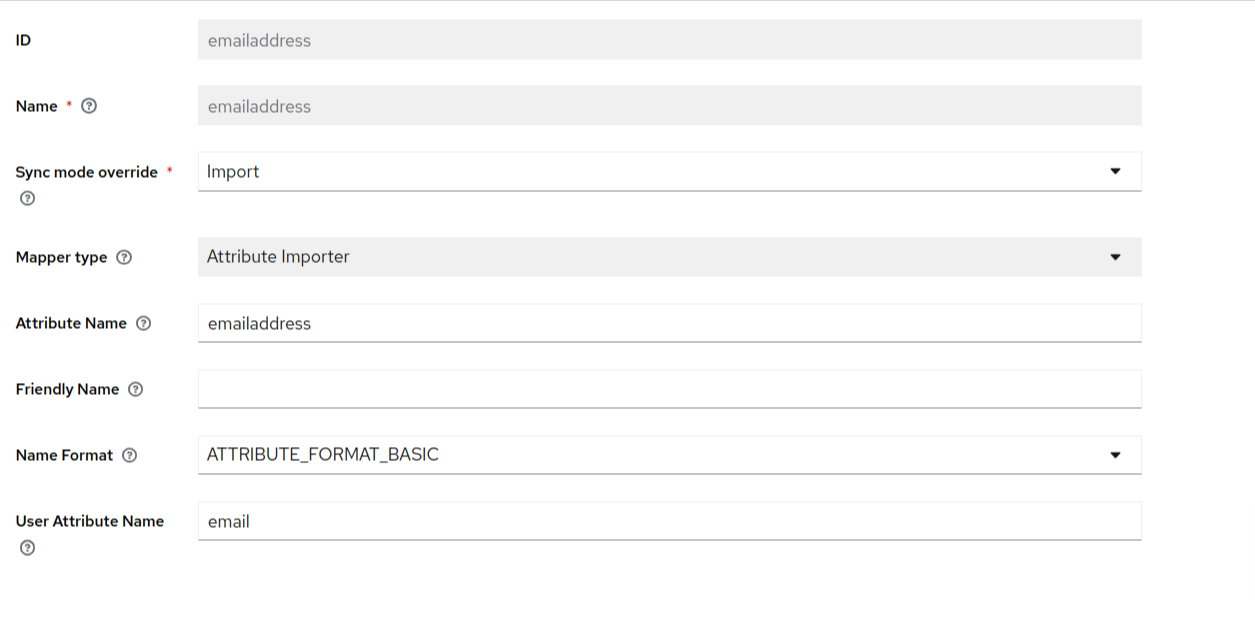
Using the above described process, create the firstname and last name mappers as well. After doing the required configurations in KeyCloak, you need to do the required setup in your external identity provider as well.
If your external IDP is Entra ID, Click Here to learn more and detailed instructions about how to setup entraid SSO.
Additional Mappers in KeyCloakIf you want to map additional fields, then in KeyCloak you can add more fields as well, using which you can map those additional attributes. Some of those fields are as follows
- Gender
- Locale
- Family Name
- Middle Name
- Birth Date
You can also create a custom attribute in KeyCloak and add that as mapper in KeyCloak. Click Here to learn more about how to add a custom attribute in your KeyCloak Realm.
Sync Mode Choices- We recommend that you make the sync mode to “Force” for the identity provider in the keycloak. This will always update the user during every login with your identity provider. However this is not mandatory. The other sync modes available in KeyCloak are as follows:
- Legacy
- Import
- Inherit
- For more information on these Sync Modes Click Here